The global financial sector is witnessing a paradigm shift in data privacy as major institutions begin integrating homomorphic encryption (HE) to facilitate secure cross-bank collaboration. By allowing computational operations to be performed directly on encrypted data without the need for decryption, this advanced cryptographic technique enables banks to share intelligence on fraud detection, anti-money laundering […]
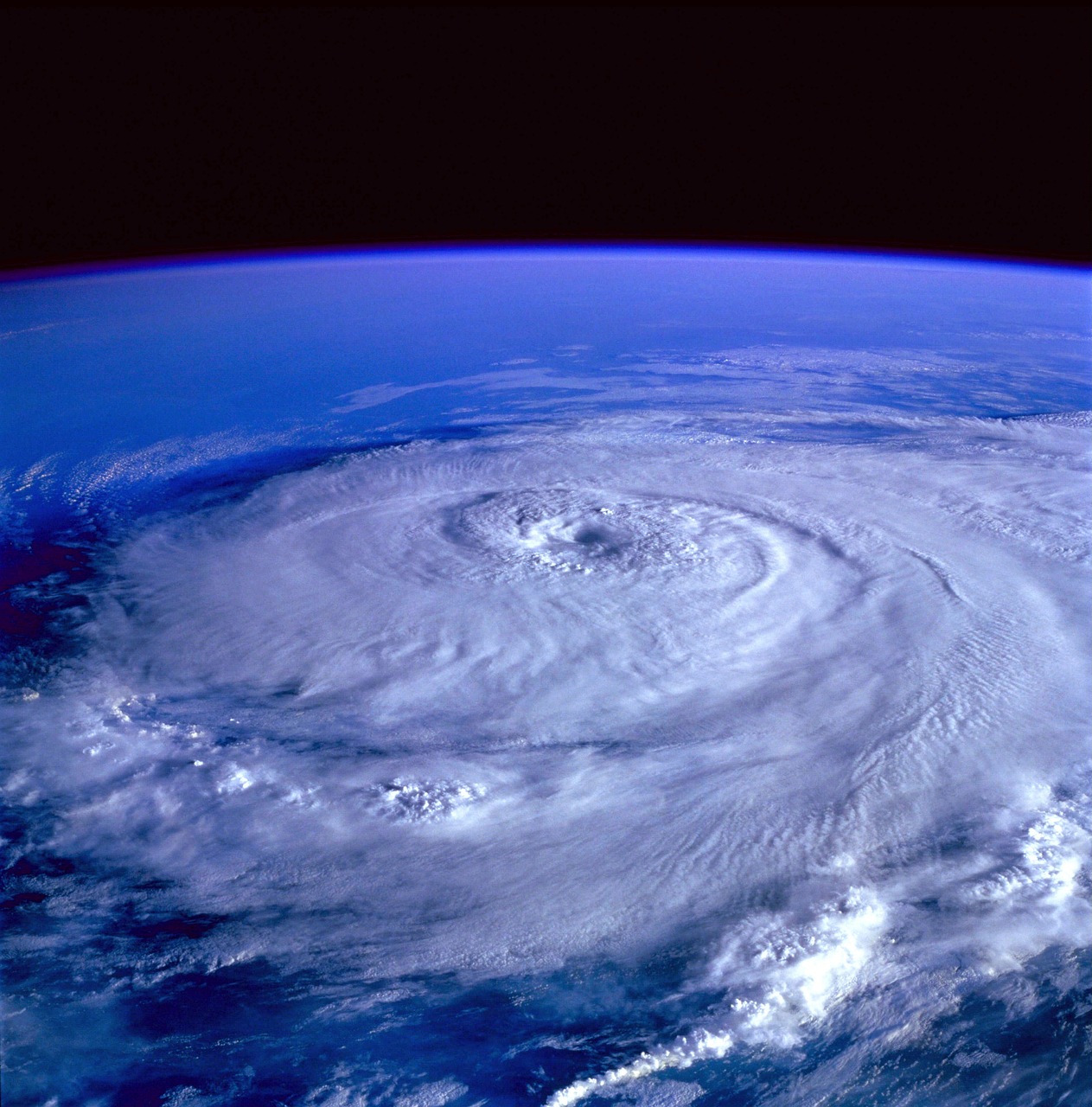
Emerging cybersecurity vulnerabilities in commercial satellite-to-ground communication networks
The rapid expansion of the global space economy has introduced a critical security paradigm shift as commercial satellite-to-ground communication networks become essential infrastructure for logistics, telecommunications, and national security. While these constellations provide unprecedented connectivity, researchers have identified a growing array of vulnerabilities within the ground station segments and the radio frequency (RF) links that […]
The Implementation of Real-Time Biometric Authentication for Cross-Border Financial Settlements
The global financial landscape is undergoing a significant transformation with the integration of real-time biometric authentication protocols for cross-border settlements. By leveraging advanced facial recognition, iris scanning, and behavioral analytics, financial institutions are effectively eliminating the reliance on traditional, vulnerable credentialing systems. This transition addresses the critical need for heightened security in high-value international transfers, […]
The Integration of Sovereign Sovereign AI Models in National Defense Infrastructure
The global defense landscape is undergoing a paradigm shift as nations increasingly prioritize the development and deployment of sovereign artificial intelligence models within their critical security infrastructure. Unlike commercial, off-the-shelf AI solutions, sovereign models are designed to operate exclusively within domestic borders, ensuring that sensitive intelligence, tactical communications, and military logistical data remain under total […]
The Proliferation of Synthetic Identity Fraud in AI-Enhanced Retail Banking
The Proliferation of Synthetic Identity Fraud in AI-Enhanced Retail Banking The rapid integration of artificial intelligence into retail banking has ushered in a new era of efficiency and customer personalization, yet it has simultaneously provided a sophisticated toolkit for financial criminals. Synthetic identity fraud, which involves the creation of a persona by combining real data—such […]
Quantum-Resistant Encryption Standards Adoption Across Global Banking Systems
The global banking sector is currently undergoing a critical architectural transformation as financial institutions begin the systematic adoption of quantum-resistant encryption standards. Driven by the looming threat of “harvest now, decrypt later” attacks—where malicious actors intercept encrypted data today with the intention of unlocking it once powerful quantum computers become viable—major central banks and commercial […]
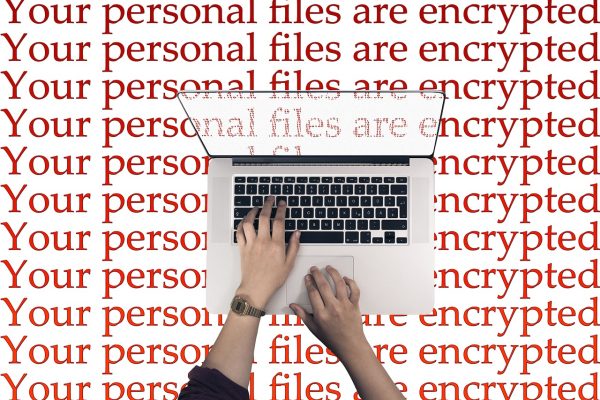
State-Sponsored Ransomware Attacks Targeting Global Renewable Energy Grids
A surge in sophisticated, state-sponsored ransomware attacks is currently targeting critical renewable energy infrastructure across the globe. Cybersecurity agencies have identified a coordinated effort by advanced persistent threat (APT) groups to infiltrate the operational technology (OT) systems of wind farms, solar arrays, and hydroelectric power stations. By deploying polymorphic ransomware strains, these actors seek to […]
The Surge in AI-Powered Phishing Campaigns Targeting Financial Institutions
Financial institutions are currently grappling with a sophisticated wave of cyberattacks as malicious actors increasingly leverage generative artificial intelligence to orchestrate large-scale phishing campaigns. By utilizing advanced large language models, cybercriminals can now generate hyper-realistic, grammatically flawless, and contextually relevant communications that mimic official bank correspondence. This technological leap has significantly lowered the barrier to […]
Integration of Neural Interface Security Protocols in Next-Gen Enterprise Hardware
As the enterprise sector pivots toward high-bandwidth neural-computer interaction (NCI) for executive productivity and technical workflow optimization, a new industry standard for neural interface security protocols has emerged. Leading hardware manufacturers are now embedding dedicated, hardware-level encryption modules designed to isolate raw neuro-synaptic telemetry from general-purpose operating systems. This architectural shift aims to mitigate the […]
Cybersecurity Threats in Submarine Data Cables
The global digital economy relies heavily on a vast, interconnected network of submarine fiber-optic cables that carry over 95% of international data traffic. While these conduits are essential for high-speed connectivity, they have increasingly become a focal point for geopolitical tension and national security concerns. Cybersecurity experts warn that the physical and digital vulnerability of […]